Finding an IP needle in a fraudstack – using Cifas’ databases to track criminal networks and prevent fraud
17 June 2019.jpg)
Sometimes, it’s not enough for a product to be great. This is particularly so if the service used to access that product is not able to adapt and evolve to the changing demands of customers.
A well-known example of this is Blockbuster. Before the early 2000s, Blockbuster dominated the video and DVD rental market. In 1997 Netflix was founded to essentially give customers access to the same product (in this case, films), the difference being it gave its customers much greater control and flexibility over when and how it could access the product.
The onset of the ‘Digital Age’ meant consumers started to want, and expect, films instantly, and without having to go to the video store to pick them up and drop them off. Blockbuster failed to adapt their service and, even though their product was essentially the same, they were decimated by new digital services coming to market.
The evolution of fraud prevention
It’s the willingness to change and develop in accordance with changes in technology and expectation that marked Cifas out as one of the key UK partners for TruNarrative early on in our own journey. We are proud to continue to work and evolve with them. Our integration with their databases means we can facilitate and support Cifas and its members with innovation around using data dynamically in preventing financial crime.
Cifas has evolved dramatically over its lifetime. Between 1988 and 2003, its members recorded their cases via credit reference agencies (CRAs) by fax or post. Then a CRA mainframe system was developed, and today cases are filed via the Fraud Investigations Database (FIND). That technology continues to evolve (a recent development is facial matching technology, for instance), but so do the methods used by those we’re fighting against – the fraudsters.
Criminals are becoming more sophisticated – they take advantage of the latest technologies and share insight with each other to streamline their attacks. However, as criminal networks grow and continue to use genuine customer information mixed with synthetic data, there are opportunities for us to detect them, providing we can see the full picture.
Criminals use different names, hide behind different IDs (genuine or fake) and build complex corporate structures to create a maze of information, which must be navigated through to have a chance of detecting them. They also live in the real world, however, and can easily trip themselves up by using common addresses (physical and electronic), telephone numbers, or – increasingly likely – IP addresses. These common threads may be at opposite ends of complex networks, and not very easy to recognise from a single data source or attribute. So how do we connect the dots?
Analysing a fraud network
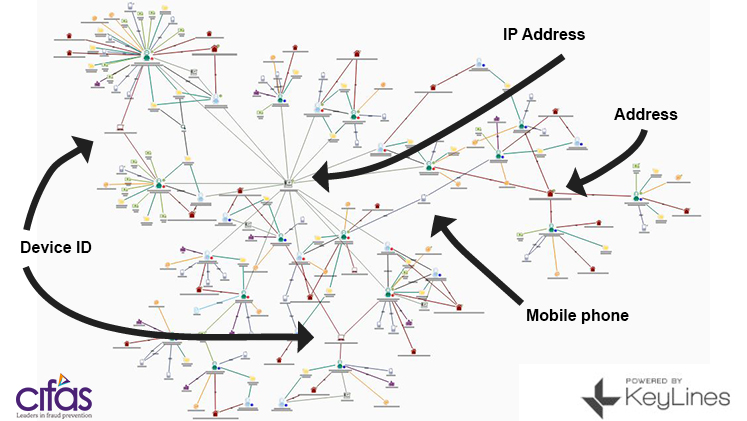
Below is a genuine recent example of a network that shows where some of these pieces of information are used to tie cases in different names together.
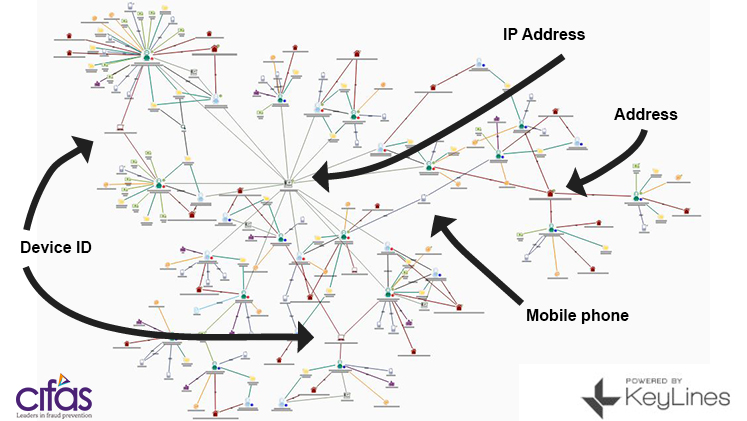
From the link analysis, we can see there are key ‘nodes’ connecting the network:
- Address;
- Mobile phone:
- Device ID.
But the one attribute that connects all the dots of the fraud network together is an IP address.
This result is only achievable thanks to Cifas’ 400+ member organisations sharing insight on its databases. But the results are only as good as the data shared – and the technology used to access and make a decision on it.
In 1989 when Cifas had just 38 organisations as members, the need to share IP addresses and device information would have been non-existent. As the online threat continues to evolve, it is essential that our use of the data reflects these risks.
Dynamic collaboration in the fight against fraud
Does your organisation continue to provide services with the around the ‘bricks and mortar’ Blockbuster approach? Or are you looking to harness the power of ‘dynamic collaboration’ – utilising new technologies fit for digital age?
‘Dynamic collaboration’ is the theme of Cifas’ Annual Conference this year, and we’ll be there to speak to anyone interested in our partnership with Cifas, and what is possible in the fight against fraud now. For example:
- Can you connect the dots? by accessing all the attributes (including IP, Device etc) available via Cifas;
- Auto decision: it is now possible in certain circumstances to build rules that automatically decline or accept where appropriate;
- Autofile: why drive back to the store to drop off your video, when you can do it online! The same principles apply to filing back to Cifas – this can be done using pre-populated forms;
- See the bigger picture: enrich Cifas insight with other complementary services, including your own data models, email, telephone, device and ‘social intelligence’ – layering these in a single environment extends the network and provides a more robust protection against fraud.
Working together on our fraud prevention strategies
TruNarrative works with many global partners in the fight against fraud, but Cifas stands alone in its principled approach and not-for-profit structure. We are proud of our partnership with Cifas and see the data it provides as a key component of any successful, layered fraud prevention strategy in the UK.
Cifas’ National Fraud Database is the UK’s largest repository of fraud risk information – information that can be accessed by its members to reduce their exposure to fraud and financial crime. But are we utilising the data and functionality to its maximum potential?
Posted by: Carl WoodburnCarl is the Client Director at TruNarrative.
PREVIOUS POSTNEXT POST
Fighting Fraud and Corruption Locally 2020
24 June 2019
Calling all local authorities! Work for 2020’s Fighting Fraud and Corruption Locally strategy is set to begin July 2019 and volunteers are needed. Collaboration from councils is vital in developing the strongest strategy possible - make sure your council is involved.
CONTINUE READING
What Glastonbury, the Chelsea Flower Show and the Rugby World Cup have in common
13 June 2019
Step one, find a cheap, last minute ticket deal. Step two, make sure it's legit!
Get Safe Online is offering advice on how you can buy tickets without getting caught out by fraudsters.
CONTINUE READING
Back to blog home >

.jpg)